I went into Midnight expecting the usual privacy chain pitch and came out with a pretty different reaction. I thought I would be reading about hidden transactions and encrypted activity and the familiar crypto script about keeping things secret. Instead I kept running into something that felt much bigger. Midnight is not just trying to protect data. It is quietly asking why so much data needs to be collected in the first place. That hit me harder than I expected.
That idea matters because the internet has developed a weird habit. Every app wants more information than it really needs. Sign up and hand over your email. Verify and hand over your ID. Use a service and leave behind a trail of metadata that says way more about you than the actual content ever did. Companies store it. Analyze it. Monetize it. Lose it in breaches. Then apologize with a press release and move on. I am not even saying that as a dramatic crypto rant. I am saying it because that has become the default business model of the digital economy.
What struck me in the Midnight paper is that it frames the problem differently. The core pitch is not just secure data storage or private transactions. It is the ability to create new applications and business models without forcing developers to collect large amounts of unrelated user data in the first place. That is a very different mindset. It is less about building a locked vault for endless data and more about not filling the vault with random stuff you never needed.
And honestly that made me laugh a little because Web2 has spent years acting like every product needs to behave like a digital vacuum cleaner. Open app. Suck in data. Keep sucking. Midnight looks at that whole logic and kind of says maybe chill.
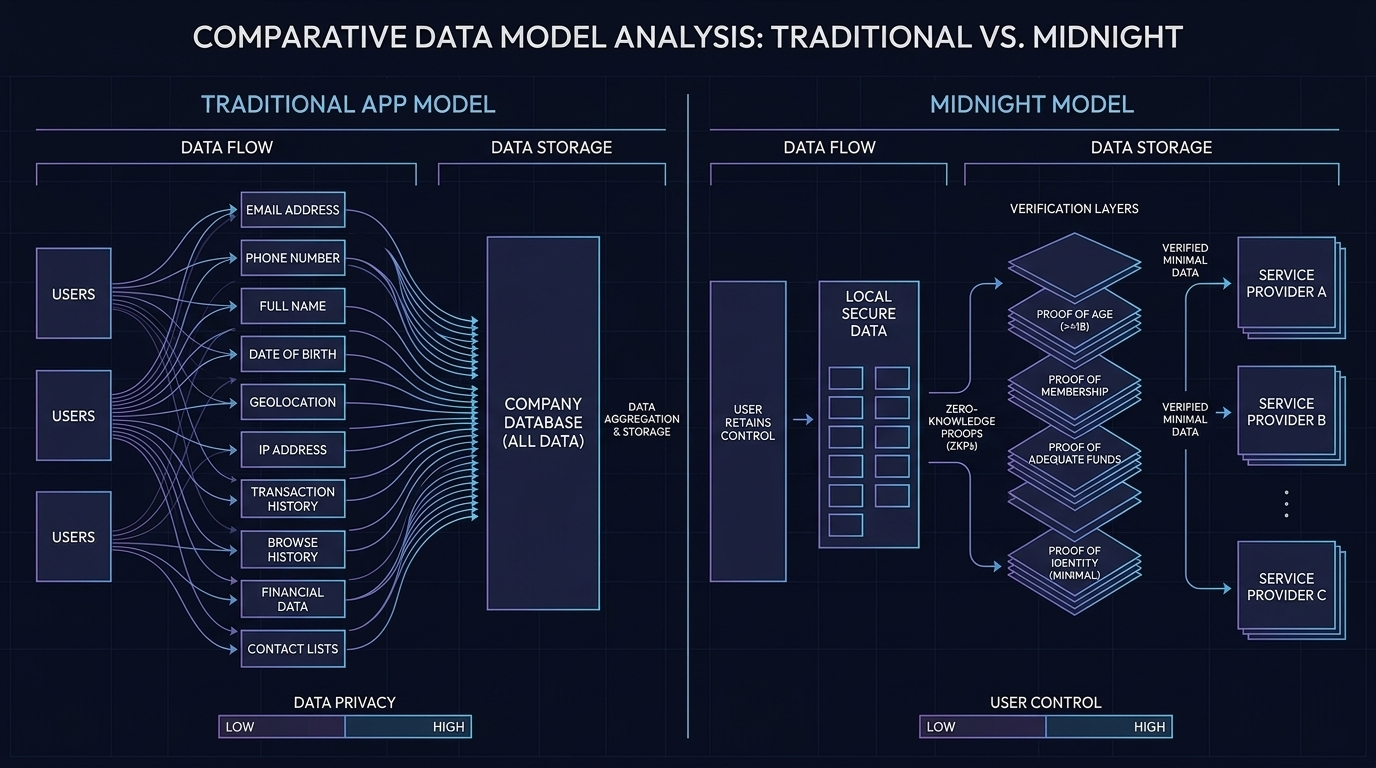
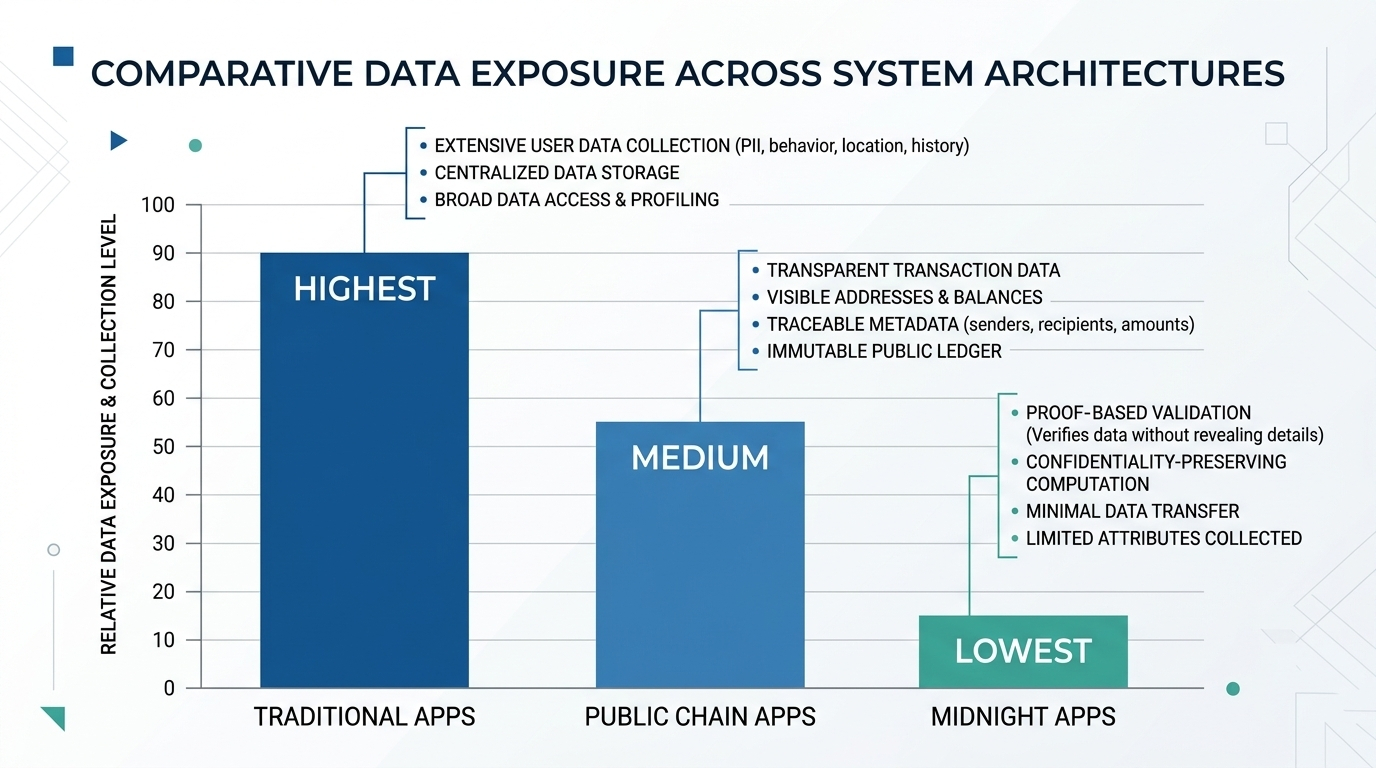
The clearest example in the paper is the visual showing regular apps versus public chain apps versus Midnight DApps. In the regular app model sensitive data gets sent across the internet and ends up with the company. In the public chain model some activity becomes publicly visible and metadata can still be correlated. In the Midnight DApp model the user keeps private data locally and the company can update smart contract state using proofs without collecting the actual sensitive information. The diagram literally ends with the company collecting no data. That is not a small tweak. That is a direct challenge to how most digital platforms are built today.
This is where my view on Midnight changed. Privacy is a useful word in crypto but it is often too narrow. It makes people think the only benefit is secrecy. Midnight seems more interesting when you see it as a data minimization system. It gives applications a way to ask for proof instead of raw information. Are you old enough. Are you qualified. Are you eligible. Did this condition get met. A lot of the time that is all a system really needs to know. It does not need your full identity file sitting on some company server like a future liability bomb.
That shift from data collection to proof collection could have bigger consequences than people realize.
Businesses today do not just hold data because they are evil cartoon villains. Some do it because they think they might need it later. Some do it because their systems were built around centralized storage. Some do it because the business model quietly rewards information hoarding. The more they know the more they can optimize targeting pricing risk scoring or monetization. That is why I think Midnight is more than a technical project. It is also an argument against a very entrenched economic habit.
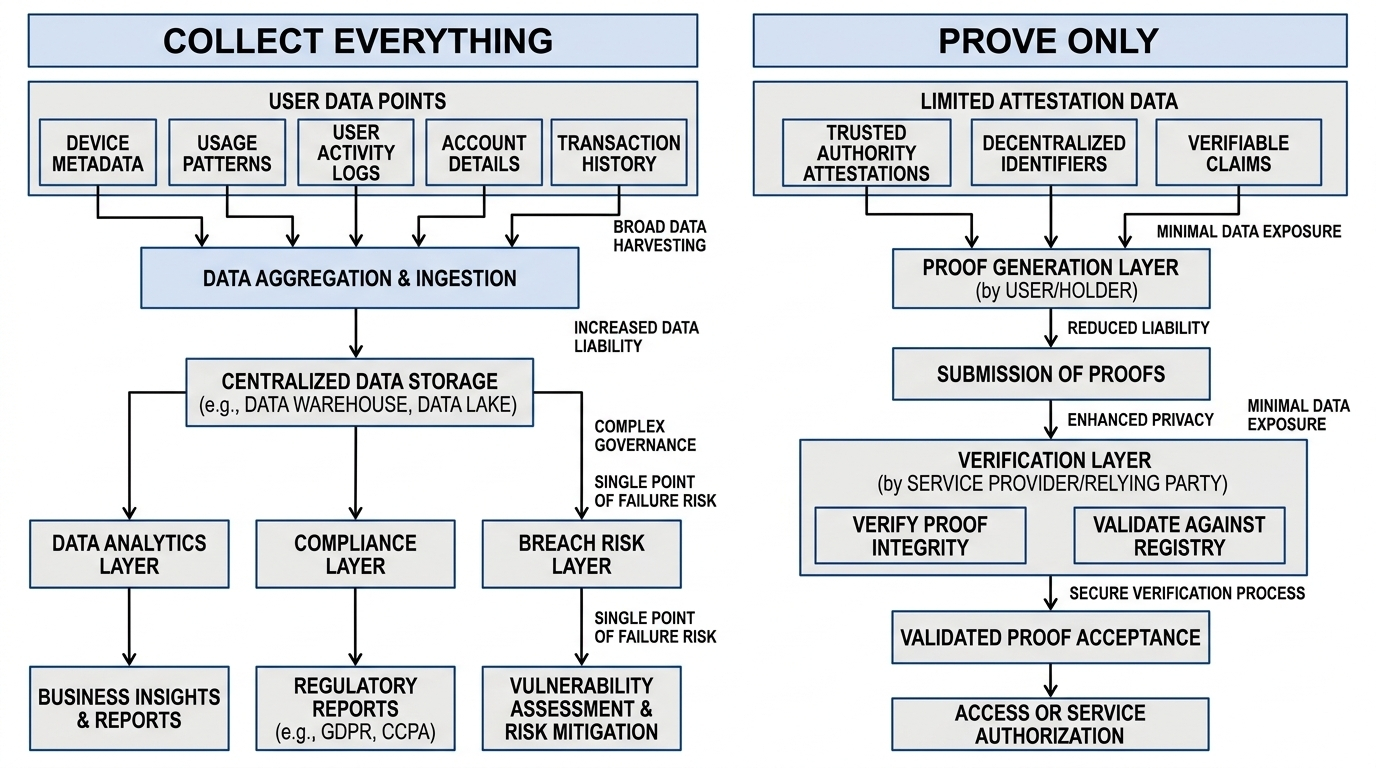
The paper leans into this by describing a world where customers want more control over their data while businesses face growing liability from leaks breaches and exposure of sensitive information and IP. That point feels very grounded. Storing data is not just an asset anymore. It is a cost center. It is legal risk. It is compliance overhead. It is a giant honeypot for attackers. Midnight’s design tries to reduce that burden by protecting user commercial and transaction metadata and by storing private data locally on the user’s machine rather than in centralized databases.
That local storage detail is one of the most underrated parts of the whole paper. I think people skip past it because it sounds technical. It is actually a massive philosophical difference. Centralized apps tend to pull your data inward. Midnight pushes private data outward toward the user. That changes the shape of the attack surface. Instead of one giant pile of information waiting to get breached you get a more distributed model where sensitive data is harder to aggregate and misuse.
There is also a business angle here that feels more important than the market is currently pricing in. Midnight says organizations can monetize business intelligence without revealing the underlying data. That line stuck with me. It suggests a world where companies can prove insights or outcomes without exposing the raw material underneath. In theory that could let businesses collaborate or extract value from data without handing over the full dataset. If that works at scale it opens a different model for data economics. Less raw extraction. More verified computation. That is a subtle shift but a serious one.
Now the critical part.
I do not think this automatically means companies will rush to collect less data. That is the uncomfortable tension underneath all of this. A lot of businesses say they care about privacy but still love data because data is leverage. It helps them understand customers more deeply and sometimes control them more effectively. So Midnight is not only offering new infrastructure. It is asking businesses to give up a habit that has been insanely profitable. That is a much harder sell than the technology itself.
And that is why I think Midnight is interesting. It is not just fighting a technical problem. It is fighting an incentive problem.
If developers actually use Midnight to design systems that ask for less information then the project could matter in a way that goes beyond blockchain. It could become part of a broader move away from surveillance style product design. That would make it relevant not only to crypto people but to anyone tired of the endless cycle of overcollection breach risk and fake consent screens nobody really reads.
Of course there are risks. Midnight still has to prove developers will build around this model. It still has to navigate policy concerns around privacy preserving systems. It still has to compete in a market where loud narratives often beat thoughtful infrastructure in the short run. There is also the classic challenge of behavior. Just because a protocol allows restraint does not mean people will choose restraint. Some teams may still collect more than they need because old habits die hard.
But I keep coming back to the same thought.
A lot of blockchain projects try to make existing systems faster cheaper or more decentralized. Midnight might be doing something stranger and maybe more important. It is questioning the assumption that useful applications must be built on top of giant pools of exposed user data.
That is why I do not see it as just another privacy chain anymore. It looks more like an attack on the collect everything business model.
And honestly that might be the sharpest thing about it.
@MidnightNetwork #night $NIGHT

