A Hack That Immediately Felt Different From the Usual DeFi Disaster
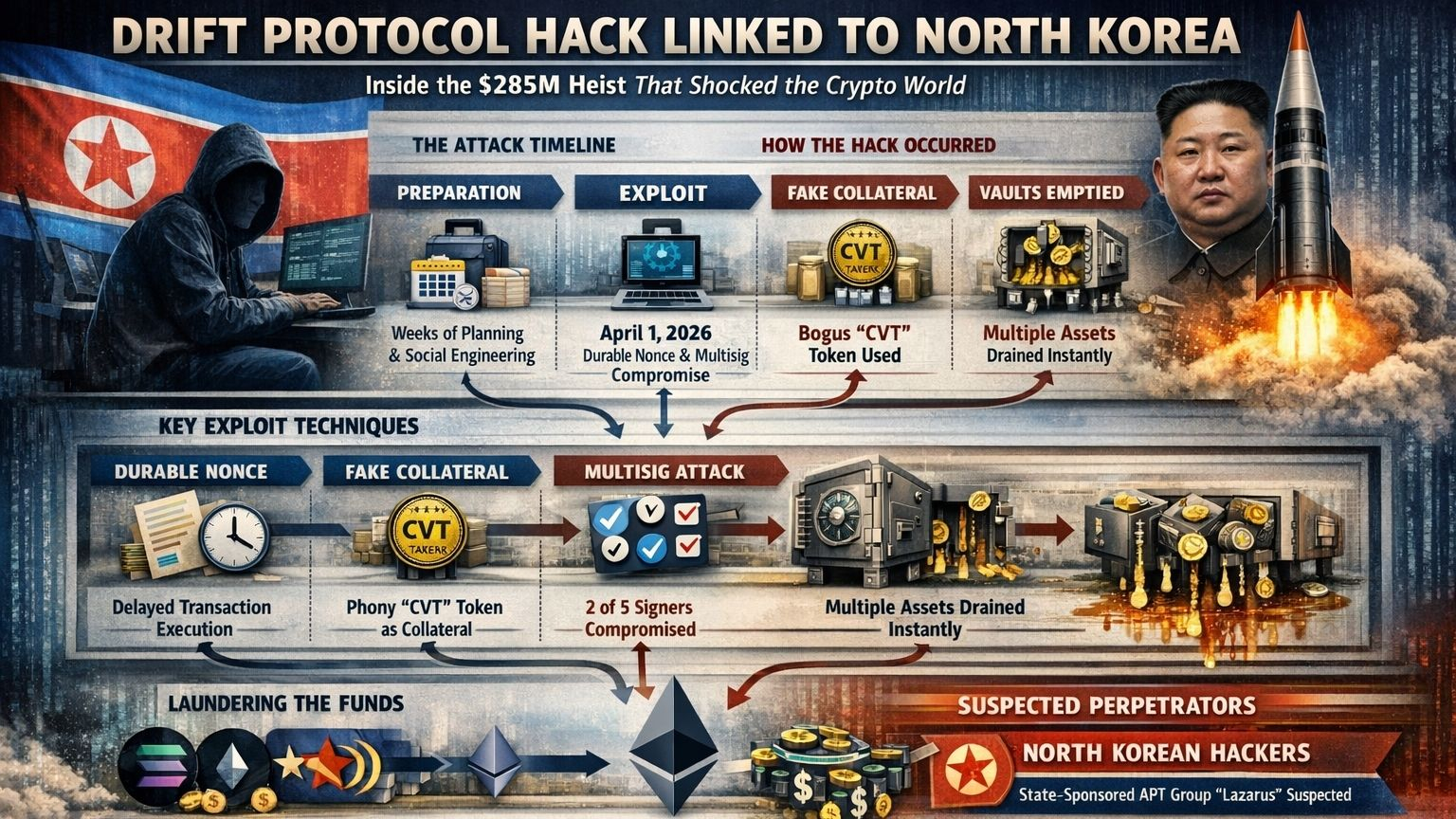
The attack on Drift Protocol on April 1, 2026, did not resemble the standard DeFi exploit in which a coding error is discovered, a vulnerable contract is paused, and the industry begins the familiar cycle of patching, blame, and retrospective wisdom. What emerged instead was a more unsettling picture in which a legitimate Solana transaction feature, compromised signer approvals, and a fast administrative takeover appear to have been woven together into a carefully staged operation that investigators now believe was likely carried out by North Korean actors. Drift said the attacker gained unauthorized access through a “novel attack involving durable nonces,” rapidly seized Security Council administrative powers, and triggered losses that outside investigators have placed at roughly $285 million to $286 million.
What makes the incident especially important is that it moved almost immediately beyond the language of ordinary exploitation and into the language of organized intrusion. Elliptic said the on-chain behavior, laundering methods, and network-level indicators were consistent with previous DPRK-linked operations, while TRM Labs said its initial investigation suggested the hack was likely perpetrated by North Korean hackers. Even before every technical step was fully settled in public, the center of gravity of the story had already changed: this was no longer just a question of whether Drift had a bug, but whether a major Solana protocol had been penetrated by an adversary operating with the patience, discipline, and post-theft laundering sophistication usually associated with a state-backed threat campaign.
What Drift Actually Said Happened
Drift’s own public framing matters because it sharply narrows what kind of event this was. The protocol said the incident was a “highly sophisticated operation” involving multi-week preparation and staged execution, and it explicitly stated that the breach did not stem from a smart contract bug or from compromised seed phrases. Instead, Drift said the attack involved “unauthorized or misrepresented transaction approvals obtained prior to execution,” likely facilitated through durable nonce mechanisms and sophisticated social engineering. That wording is crucial because it suggests the protocol’s codebase was not the primary weakness; the decisive failure point appears to have been the way high-privilege approvals were obtained and later executed.
Drift also confirmed the practical impact in unusually stark terms. Deposits and withdrawals were suspended during containment, and the protocol said funds placed into borrow/lend, vault deposits, and trading balances were affected. The protocol further said it was working with security firms, exchanges, bridges, and law enforcement to trace and freeze stolen assets. That response language showed two things at once: first, that the scale of the theft was immediately visible; and second, that the team understood this was not the kind of incident that could be contained inside the usual DeFi perimeter once funds had already begun moving across chains.
Why Durable Nonces Became the Center of the Story
Durable nonces are not a flaw in Solana, and that point is worth making clearly because a lot of fast commentary tends to confuse exploited features with broken features. Under normal conditions, Solana transactions rely on a recent blockhash and expire quickly if they are not broadcast in time. Durable nonces replace that short-lived blockhash with a value stored in a dedicated account, which allows a signed transaction to remain valid until the nonce is advanced. In legitimate workflows, this makes delayed or offline signing possible and can support more complex operational procedures. In the Drift incident, investigators say that same feature appears to have created a dangerous separation between the moment approvals were obtained and the later moment when those approvals were executed.
BlockSec’s reconstruction is especially helpful here because it explains the temporal dimension of the exploit in concrete terms. The firm said the attacker induced two of five Security Council multisig signers to pre-sign malicious governance transactions, then held those signed approvals until the chosen execution window. Because the Security Council was operating as a 2-of-5 Squads multisig with zero timelock, the attacker was able to move from hidden approval to immediate administrative action with almost no defensive buffer once the operation began. This is why the exploit feels structurally more serious than a conventional contract bug: the attacker did not need to discover a broken instruction in the code if they could instead secure valid signatures that would still remain executable later.
The deeper lesson is uncomfortable because it sits in a space crypto often prefers not to examine too closely. A signature is usually treated as the ultimate expression of intent, but the Drift attack appears to show that a valid signature does not necessarily mean the signer fully understood the future context in which that authorization would be used. Once a transaction is valid and can wait indefinitely for execution, the real security question is no longer limited to who signed it; it also becomes when it can execute, under what surrounding conditions, and whether the signer actually recognized the latent authority embedded in the request. That is exactly why outside security commentary described the incident less as a cryptographic failure and more as a failure of transactional policy and operational discipline.
How the Administrative Takeover Appears to Have Unfolded
The best-supported public reconstruction comes from a combination of Drift’s own statements and third-party technical analysis. BlockSec said the attack involved manipulated multisig approvals and durable nonce exploitation, ultimately transferring administrative control of Drift’s Security Council. It noted that on April 1, Drift performed a legitimate test withdrawal from the insurance fund, and then roughly a minute later the attacker submitted the pre-signed attack transactions. That timing suggests real-time monitoring and careful operational judgment rather than improvisation, because the attacker appears to have waited for a normal on-chain action to confirm that the environment was behaving as expected before moving into the decisive stage.
SecurityWeek, drawing on additional analysis, described the visible theft phase as astonishingly fast. Its report said the attackers had prepared infrastructure and multiple nonce-based transactions in advance, took over an admin key, and then drained five vaults within seconds. It also cited analysis indicating that a new wallet had been prepared days before the exploit and that the operation included multiple microtransactions and pre-positioned tooling to ensure the attack could unfold at speed once control had been obtained. Even allowing for the fact that different firms may measure slightly different points in the timeline, the picture is consistent across sources: the on-chain drain was not the beginning of the exploit but the final, compressed expression of a much longer preparation phase.
TRM Labs extends that timeline further backward. It said on-chain staging began on March 11, nearly three weeks before the April 1 execution, and described a coordinated setup involving attacker infrastructure, token manufacturing, and social engineering unfolding in parallel. That framing matters because it moves the incident out of the category of opportunistic exploitation. A campaign that begins weeks earlier, uses hidden authorization paths, and culminates in a narrow execution window is not merely technically competent; it is operationally disciplined in a way that more closely resembles a deliberate intrusion set than a lucky theft.
The Disputed but Important Question of Fake Collateral and Oracle Abuse
One of the more dramatic parts of the public reconstruction comes from TRM and later reporting that cites external forensic work, and it deserves careful handling because this is the portion of the story where the public narrative is more detailed than Drift’s own initial statement. TRM said the attacker manufactured a fictitious asset called CarbonVote Token, or CVT, seeded a thin market for it, and then used that engineered appearance of legitimacy to have Drift’s systems treat it as collateral worth hundreds of millions of dollars. In TRM’s version, the attacker was then able to list CVT as valid collateral, raise withdrawal limits, deposit vast quantities of that synthetic value, and execute 31 withdrawals over roughly 12 minutes, draining real assets such as USDC and JLP from the protocol.
SecurityWeek reported a similar sequence, stating that the attackers used the compromised admin key shortly before the heist to create a fake collateral market for CVT, modify parameters to maximize its borrowing value, and disable or effectively neutralize protective circuit breakers that were designed to stop unusually rapid vault drains. In that description, the exploit was not merely an admin takeover in the abstract; it was an admin takeover used to rewrite the economic rules of the protocol just long enough to convert a worthless internal setup into claims on real assets.
This part of the story is important because it changes how one interprets the theft. If these reconstructions are substantially correct, then the exploit was not just about access control and signer compromise. It was about using privileged access to manufacture a fake market reality inside the protocol, one in which an invented token could momentarily appear valuable enough to support enormous withdrawals. Since Drift’s initial public statement focused more on nonce-based approvals and the Security Council takeover than on the full collateral mechanics, the safest reading is that the fake-collateral sequence is a strong investigative finding rather than the final canonical account. Even so, the convergence across TRM and other reporting means it cannot be dismissed as fringe speculation.
Why Investigators Suspect North Korea
The attribution question matters here not for sensational value but because it helps explain the shape of the operation. Elliptic said it identified multiple indicators linking the exploit to the DPRK and argued that the on-chain behavior, laundering methodologies, and network-level indicators were consistent with previous DPRK-attributed operations. It added that if confirmed, the attack would represent the eighteenth DPRK act it had tracked in 2026 and would continue what it described as a broader campaign of large-scale crypto theft that the U.S. government has linked to funding for North Korea’s weapons programs.
TRM Labs reached a similar conclusion from a somewhat different angle. It said its initial investigation suggested the hack was likely perpetrated by North Korean hackers and highlighted the long staging period, the parallel setup of infrastructure and manipulation tools, and the rapid movement of funds off Solana and onto Ethereum within hours. That combination of disciplined preparation, carefully chosen timing, and immediate cross-chain laundering is exactly the sort of pattern that pushes attribution away from freelance opportunists and toward actors who already have an established operating model in large crypto thefts.
It is also worth noticing that no public source cited here claims attribution based on a single decisive indicator. The case is cumulative. Investigators are drawing on wallet behavior, laundering routes, infrastructure patterns, timing, and resemblance to previous campaigns. In crypto forensics, that is often what strong attribution looks like: not a dramatic confession or a single exposed key, but a dense cluster of operational similarities that becomes difficult to explain away as coincidence. In Drift’s case, the consistency between Elliptic and TRM is what gives the North Korea theory real weight.
The Laundering Path After the Theft
The way the stolen assets moved after the exploit is one of the strongest reasons investigators were willing to speak with relative confidence. Elliptic said the attacker systematically drained liquidity from multiple protocol vaults, converted much of the stolen asset mix into USDC through a Solana-based DEX aggregator, and then bridged the funds to Ethereum, where they were swapped into ETH. Elliptic also emphasized that because the theft involved more than 15 types of tokens across several vaults, tracking the full scope of the exploit required clustering associated Solana token accounts rather than treating each asset address as unrelated. That kind of multi-asset, cross-chain post-processing is familiar territory in professional laundering operations, and it is one reason the firm linked the activity to prior DPRK-style methods.
TRM’s description aligns with that general pattern. It said most of the stolen funds were bridged to Ethereum within hours, reinforcing the idea that the attackers were not merely trying to escape the immediate blast radius of the Solana ecosystem but were moving into a cross-chain laundering path prepared ahead of time. Once funds move into that phase, response options narrow quickly, which explains why Drift said it was coordinating not only with security firms but also with exchanges, bridges, and law enforcement almost immediately after the exploit became public.
Why This Was Not Just a Smart Contract Story
There is a tendency in crypto to reduce every large loss to a code problem because code problems feel conceptually clean. They can be audited, reproduced, patched, and placed inside the comforting technical narrative that more rigorous engineering will eventually solve everything. The Drift incident resists that simplification. Drift itself said there was no evidence of a smart contract bug and no evidence of mnemonic compromise. The mechanics described by investigators instead point toward a layered failure involving signer trust, transaction comprehension, governance design, execution policy, and operational security around high-privilege actions.
That matters because it expands the security perimeter for every large protocol. If a system’s ultimate safety depends not only on immutable contracts but also on a Security Council, a 2-of-5 multisig, zero-timelock admin powers, and signers who can be induced to approve delayed transactions they do not fully interpret, then the real attack surface is much broader than the code repository. In that world, the most dangerous vulnerability may not be a bug buried in smart contract logic but a governance workflow whose cryptographic validity hides its strategic fragility. Drift is important precisely because it makes that reality difficult to ignore.
The Scale of the Damage and Why the Incident Matters Beyond Drift
By the numbers alone, the exploit immediately entered the top tier of crypto thefts. TRM called it the largest DeFi hack of 2026 and the second-largest exploit in Solana’s history, behind only the 2022 Wormhole bridge hack. Elliptic similarly described the incident as the largest DeFi hack of the year so far and reported that Drift’s total value locked collapsed sharply in the aftermath. Whatever exact figure one prefers within the narrow range reported publicly, the order of magnitude is clear: this was not an edge-case loss confined to a minor protocol. It was a systemic event for one of Solana’s major DeFi venues.
That scale is important because attacks of this kind travel psychologically through the market far beyond the directly affected users. Every protocol with a security council, a signer set, an emergency authority path, a timelock exemption, or a delayed transaction workflow now has a reason to study Drift in detail. Even protocols on other chains should pay attention, because the underlying lesson is not uniquely Solana-specific. The exploited primitive may have been durable nonce execution, but the broader vulnerability was the gap between formal authorization and genuine situational understanding. Any system that lets powerful approvals persist into a later, less visible execution context is potentially exposed to a variation of the same logic.
What the Drift Exploit Says About the Next Phase of Crypto Security
The strongest reading of the Drift incident is that crypto has moved into a phase where the most dangerous attackers are no longer limited to finding technical flaws in protocols. They can also work across human trust, transaction design, governance structures, cross-chain liquidity paths, and time itself. Durable nonces mattered here because they turned approval into a delayed weapon. Zero timelock mattered because it removed the pause that might have exposed the malicious sequence in time. Social engineering mattered because the attacker did not need to brute-force a signature if they could instead obtain one under false or misleading circumstances. Laundering mattered because the theft was meaningful only if the value could be moved rapidly into harder-to-freeze forms across other networks.
That is why this story should not be read as a narrow tale about one unlucky protocol. It is a warning that the next generation of major crypto incidents may increasingly look like hybrid operations in which code, governance, user experience, and organizational security can no longer be separated cleanly. Drift’s investigation matters because it suggests that the decisive battlefield is shifting away from isolated software defects and toward the messy edge where cryptographic validity intersects with human judgment. Once that becomes the attack surface, the question is no longer only whether the contracts are safe. It is whether the people entrusted with extraordinary permissions can still recognize when a routine approval has been transformed into an irreversible strategic compromise.