
I used to think storage was just a technical decision.
On-chain meant trust and permanence. Off-chain meant flexibility and scale. You choose based on constraints and move on.
But once you start looking at SIGN through the lens of attestations, storage stops being a simple infrastructure choice. It becomes a decision about how much of the original truth a system is able to carry forward over time.
Because an attestation is not just data. It is something that will be verified later, often in a different context, by a system that was not present when it was created.
That’s where the differences between models start to matter.
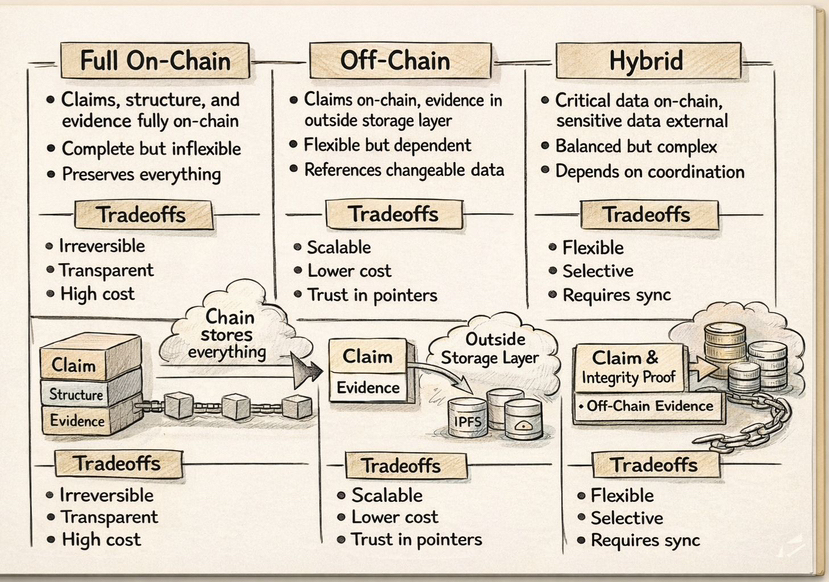
With full on-chain storage, everything is embedded directly into the system. The claim, the supporting data, and the structure all live together. Verification is straightforward because nothing needs to be fetched or reconstructed. The chain becomes the single source of truth.
At first, this feels like the most reliable option.
But over time, it starts to reveal a limitation. Not every part of a claim needs to be permanently exposed in order to remain verifiable. By placing everything on-chain, the system preserves more than what is actually required. Sensitive or contextual information becomes part of a permanent record, even if it was only relevant at the moment of issuance.
In this model, nothing is lost but nothing can be selectively forgotten either.
Off-chain storage, using systems like Arweave or IPFS, separates the claim from its underlying data. The attestation on-chain contains a reference, typically a hash or identifier, while the full evidence is stored externally.
This reduces on-chain load and allows systems to scale more efficiently. It also creates a layer of abstraction between verification and exposure. A verifier can confirm that the data exists and matches the claim without necessarily interacting with the full dataset.
But this separation introduces dependency.
The attestation now relies on an external layer to remain accessible and meaningful. The reference remains constant, but the interpretation of what it points to can change depending on how that data is accessed, versioned, or understood over time.
The system verifies integrity, but not necessarily context.
Hybrid models attempt to balance both approaches. Critical elements such as schema definitions, issuer signatures, and verification logic remain on-chain, while larger or sensitive data is stored externally.
This design provides flexibility while maintaining a verifiable core.
However, hybrid systems are not simply a middle ground. They depend on coordination between multiple layers. The schema defines structure, the issuer defines authority, the storage layer holds evidence, and the verifier decides acceptance. Each of these components can evolve independently.
Over time, the consistency between them becomes the real challenge.
This is where the question shifts.
It is no longer about whether data should be stored on-chain or off-chain. It becomes a question of what part of the attestation needs to remain independently verifiable, even if everything else around it changes.
Because different storage models age differently.
An on-chain attestation preserves its entire context, even when parts of that context are no longer relevant.
An off-chain attestation preserves integrity, but depends on external systems to maintain accessibility and meaning.
A hybrid attestation depends on alignment between multiple layers, and alignment is rarely permanent.
SIGN does not enforce a single approach. It allows developers to decide what should be anchored directly and what can remain external.
That flexibility is powerful, but it also means that two attestations with similar structure can behave very differently over time.
One may carry enough information to remain fully self-contained. Another may rely on external layers that were stable at the time of issuance but may not remain so indefinitely.
Both are valid. But they do not carry the same guarantees.
This is why storage in SIGN is not just about location. It is about durability of meaning.
An attestation does not fail when its hash breaks or its signature becomes invalid. Those are easy to detect. The harder problem is when everything still verifies correctly, but the surrounding context has shifted enough that the original meaning no longer fully applies.
The system continues to function. The claim continues to resolve. But what is being verified is no longer exactly what was intended at the time it was created.
So the real decision is not technical.
It is about choosing what you are willing to let drift.
Because in the end, every storage model preserves something and allows something else to change.
